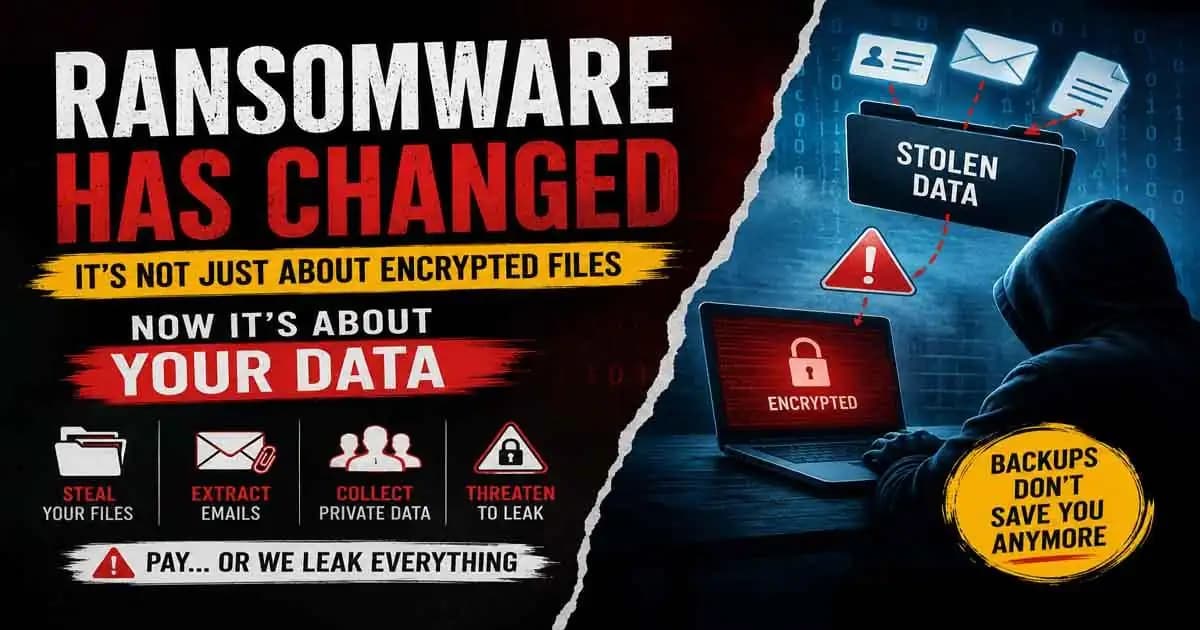
Ransomware has changed dramatically by 2026, and many people still picture it the old way: a screen suddenly locking up, files becoming unreadable, and attackers demanding payment to restore access. That still happens but it is no longer the entire story.
Today, many ransomware attacks begin quietly, long before encryption appears. By the time victims notice something is wrong, sensitive data may already be copied, transferred, and prepared for public exposure.
This shift has changed how businesses, schools, hospitals, and even small organizations experience cyberattacks. The real pressure often no longer comes from locked files alone. It comes from the fear of private information being leaked online.
Modern Ransomware Attacks Often Begin Silently
A common situation now starts with what seems like a routine event. An employee receives an email that looks legitimate. A remote login portal is exposed with a weak password. An old server misses a Security patch.
Nothing immediately crashes.
Systems continue working normally for days or even weeks while attackers quietly move through the network.
Modern ransomware groups often spend time exploring internal systems before launching the visible part of the attack. During that period, they search for valuable information:
- Customer databases
- Financial records
- Internal emails
- Employee documents
- Identity records
- Confidential communications
Only after collecting enough information do many attackers deploy ransomware encryption.
That timing is intentional.
Why Cybercriminals Changed Their Strategy
Years ago, organizations mainly worried about restoring files from Backups. If backups existed, recovery was painful but possible.
Cybercriminals noticed this.
As more companies improved backup systems, attackers adapted their methods.
Now the threat sounds different:
“Pay us, or we publish your data.”
This approach is commonly called data extortion, and it has become one of the defining characteristics of modern ransomware operations.
The reason it works is psychological as much as technical.
Even when a company successfully restores encrypted systems, the stolen data still exists somewhere outside its control.
Sensitive emails may contain confidential conversations. Internal documents may reveal business strategies. Customer records may include addresses, phone numbers, or financial details. Employee information may expose payroll or identity documents.
Why Data Theft Creates Long-Term Damage
For healthcare providers, leaked records can expose highly personal medical information. For schools, it may involve student data. For businesses, it can damage trust with customers and partners almost instantly.
In many recent incidents, organizations restored their systems but still faced weeks or months of fallout because attackers threatened to release stolen information publicly.
That is what makes modern ransomware different from older perceptions of cybercrime.
The attack is no longer just about operational disruption. It is also about:
- Reputation damage
- Privacy exposure
- Legal consequences
- Extortion pressure
- Long-term trust issues
Attackers understand this extremely well.
Ransomware Groups Now Operate Like Organized Businesses
Some ransomware groups now operate almost like professional organizations.
Security (1) researchers and law enforcement agencies such as the FBI, Europol, and CISA have repeatedly warned that cybercriminal groups increasingly combine intrusion, surveillance, data theft, extortion, and public leak strategies into one coordinated operation.
In some cases, attackers even create dedicated leak websites where stolen files are published if victims refuse payment.
This creates pressure from multiple directions at once.
A company may be trying to restore systems while also handling:
- Customer concerns
- Legal reporting requirements
- Media attention
- Internal panic
- Regulatory investigations
Even organizations with good backups can still face enormous damage because the exposure risk cannot simply be “restored” away.
How Most Modern Ransomware Breaches Begin
One reason these attacks continue to grow is that many entry points remain surprisingly ordinary.
Phishing Emails
Phishing emails are still one of the most common starting points. A fake invoice, login request, Delivery notification, or document-sharing email can trick someone into revealing credentials or downloading malicious software.
Weak Passwords
Weak passwords remain a major issue, especially when reused across services. Attackers frequently rely on stolen credentials purchased from previous breaches or gathered through phishing campaigns.
Exposed Remote Access
Once attackers gain access to a remote desktop system, VPN account, or cloud platform, they may quietly expand deeper into the environment.
Unpatched Vulnerabilities
Organizations often delay updates because systems are critical or difficult to interrupt. Attackers know this and actively scan the internet for exposed systems running outdated software.
Remote Work Expanded the Attack Surface
Remote work has also changed the security landscape.
Employees now connect from homes, personal devices, shared networks, and mobile environments far outside traditional office infrastructure.
That flexibility improved productivity for many organizations, but it also expanded the number of potential attack surfaces.
By 2026, cyberSecurity again experts increasingly describe ransomware as a full-scale intrusion process rather than a single malware event.
The encryption stage is often just the final act.
Why Backups Alone Are No Longer Enough
This evolution has changed how organizations think about defense.
For years, backups were considered the central ransomware protection strategy. Backups are still essential, but they are no longer enough by themselves.
If attackers steal sensitive information before encryption begins, restoring files does not eliminate the broader consequences.
That is why many security teams now focus heavily on limiting data exposure in the first place.
What Organizations Are Doing to Reduce Risk
Multi-Factor Authentication (MFA)
Multi-factor authentication has become one of the most important defenses because stolen passwords alone are often insufficient when MFA is properly enabled.
Security Monitoring
Security monitoring tools are increasingly used to detect unusual behavior, such as:
- Large file transfers
- Suspicious login locations
- Unexpected privilege escalation
- Unusual internal network activity
Network Segmentation
Instead of allowing broad access across internal systems, organizations try to isolate sensitive environments so attackers cannot move freely after gaining entry.
Offline Backups
Offline backups remain critical because ransomware often attempts to encrypt or destroy connected backup systems first.
Keeping protected copies disconnected from the main network can significantly improve recovery options.
Human Behavior Still Plays a Major Role
Employee awareness matters more than many people realize.
Modern phishing campaigns are no longer always obvious. Attackers increasingly use realistic branding, conversational language, AI-generated writing, and even compromised email accounts from trusted contacts.
Many malicious emails now look more convincing than the obvious scams people learned to recognize years ago.
That means cybersecurity is no longer only a technical problem handled by IT departments.
Everyday decisions clicking links, approving login requests, reusing passwords, ignoring software updates can directly influence organizational risk.
Smaller Businesses Are Increasingly Targeted
Experts increasingly warn against assuming ransomware only targets large corporations.
Smaller businesses are often attractive precisely because they may have fewer security resources.
Schools, local governments, clinics, nonprofits, and mid-sized companies frequently face significant pressure during attacks because operational disruption affects real people immediately.
Cybercriminals know that urgency can increase the likelihood of payment.
Data Breach Laws Are Changing the Impact of Attacks
Another important shift is the growing overlap between ransomware and data breach disclosure laws.
In many regions, organizations that experience data theft may face regulatory reporting obligations even if systems are eventually restored.
Legal consequences can emerge from the exposure of personal information itself.
This creates a difficult reality for victims.
Recovering operations may only be the beginning of the problem.
Modern Ransomware Is Really About Leverage
The broader lesson from modern ransomware is that data itself has become the primary leverage point.
Files are valuable not only because organizations need access to them, but because attackers understand how damaging exposure can be.
Private communications, financial information, intellectual property, identity records, and internal documents can all be weaponized to create fear and pressure.
That is why cybersecurity conversations in 2026 increasingly focus on resilience rather than simple prevention.
No organization can guarantee perfect protection. But reducing attack opportunities, limiting lateral movement, detecting suspicious activity early, and protecting sensitive data can dramatically reduce the impact of an incident.
Modern ransomware attacks are designed to exploit trust, urgency, and exposure simultaneously.
And increasingly, the most dangerous part of the attack may happen before anyone even realizes the breach has started.
FAQ
What is data extortion in ransomware attacks?
Data extortion is when attackers steal sensitive information before encrypting systems and then threaten to leak the data publicly unless payment is made.
Can backups fully protect against modern ransomware?
Backups are still extremely important, but they do not solve the problem of stolen data. Attackers may still leak sensitive information even after systems are restored.
How do most ransomware attacks begin?
Many attacks begin through phishing emails, stolen passwords, exposed remote access systems, or unpatched software vulnerabilities.
Why are smaller businesses targeted by ransomware groups?
Smaller organizations often have fewer cybersecurity resources and may feel stronger pressure to pay quickly when operations are disrupted.
Is ransomware only about encrypting files now?
No. Modern ransomware operations increasingly focus on stealing sensitive data, applying extortion pressure, and damaging trust or reputation in addition to encryption.