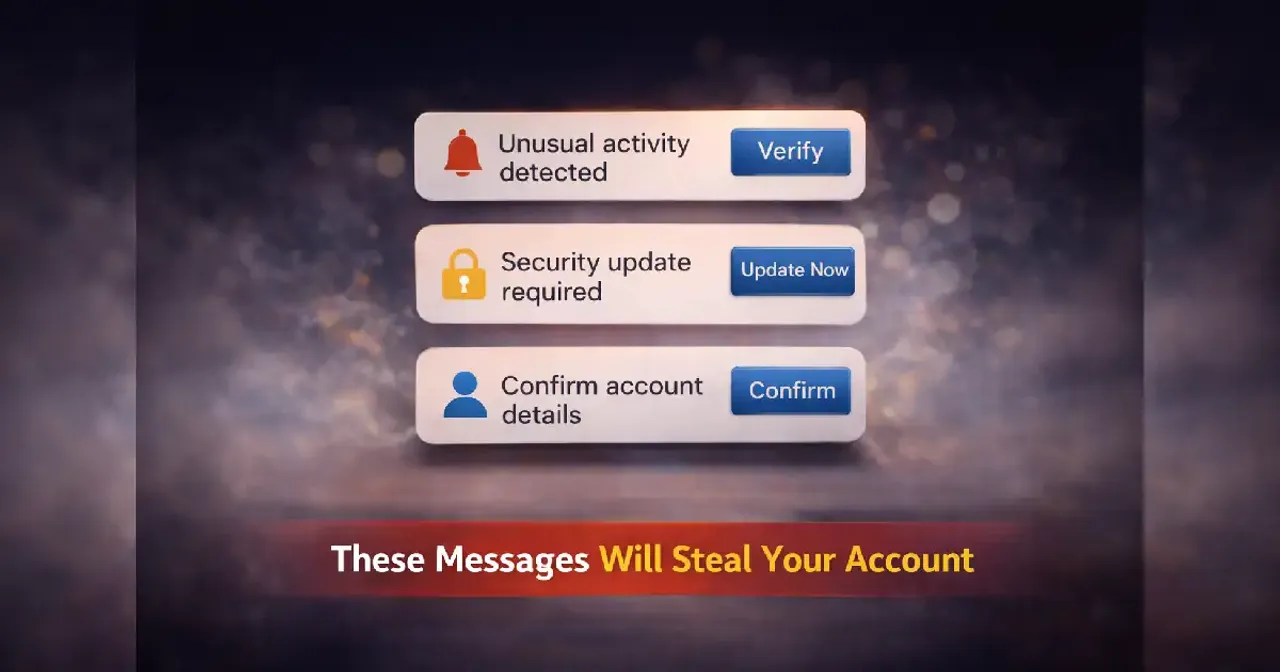
account stealing messages rarely look dangerous. They arrive quietly, wrapped in familiar language, polite tone, and visual cues we’ve been trained to trust. No flashing warnings. No obvious mistakes. Just a message that feels routine enough to follow without thinking and that’s exactly where the risk lives.
Most people imagine account theft as something dramatic: suspicious links, broken grammar, urgent threats. In reality, the messages that work best are the ones that feel normal. They don’t interrupt your day. They blend into it.
The calm surface that lowers your guard
One of the most effective tricks behind these messages is emotional neutrality. They don’t rush you. They don’t scare you. They sound administrative, almost boring.
“Unusual activity noticed.”
“Please confirm your details.”
“Action required to avoid disruption.”
These phrases don’t trigger panic. They trigger compliance.
Our brains associate calm, measured language with legitimacy. When a message sounds like it came from a support desk or internal system, skepticism fades. The absence of drama feels like proof of authenticity.
Ironically, the calmer the message, the easier it is to trust.
Familiar formats we stop questioning
Over time, digital life teaches us patterns. We learn what a “normal” notification looks like. Where logos appear. How customer support messages are structured. Which buttons feel expected.
Account-stealing messages copy these patterns carefully.
They don’t need to be perfectjust familiar enough to pass a quick mental check. Once a format matches something we’ve seen before, our brains stop analyzing details and start filling in assumptions.
“This looks like what I usually get.”
“So it must be real.”
That assumption is powerful, and attackers know it.
Authority without accountability
Many deceptive messages lean heavily on implied authority. Not specific people. Not verifiable contacts. Just roles and departments.
“Security Team.”
“Account Services.”
“System Administrator.”
These labels sound official but are intentionally vague. They create hierarchy without traceability.
Humans are wired to respect authority signals. When a message claims to represent a system larger than us, questioning it feels unnecessaryor even inappropriate.
What’s missing is a clear path to verification. And that absence often goes unnoticed.
The psychology of helpfulness
Another overlooked factor is how these messages frame themselves as assistance rather than demand.
They’re not stealing from you. They’re helping you fix a problem.
“We noticed something unusual.”
“We want to keep your account secure.”
“We’re reaching out to protect your access.”
This positioning flips the dynamic. The sender appears responsible and proactive. You become the beneficiary.
Helping behavior is deeply ingrained. When someone seems to be doing you a favor, resistance feels rude. Responding feels cooperative.
And cooperation, in this context, is the opening attackers need.
Specific details that feel convincing
Many account-stealing messages include just enough personalized detail to feel real. A partial username. A device type. A location that sounds plausible.
These details don’t need to be accurate. They need to be believable.
The human brain equates specificity with effort, and effort with legitimacy. We rarely stop to ask where the information came fromonly whether it sounds right.
Once that box is checked, scrutiny drops sharply.
Why repetition makes it worse
Trust isn’t built in a single interaction. It accumulates.
If you receive similar-looking messages over timefrom real platforms, apps, servicesyou internalize the template. That template becomes your reference point.
So when a deceptive message matches the template, it doesn’t feel new. It feels expected.
This is why awareness campaigns alone aren’t enough. They often show extreme examples, while real threats live in the gray area of normalcy.
The role of divided attention
Most people don’t read messages in ideal conditions. They skim while multitasking. Between meetings. While commuting. During moments of mental fatigue.
Under cognitive load, the brain relies on shortcuts. Tone, layout, and familiarity matter more than logic.
Account-stealing messages are designed for these moments. They don’t require deep engagementjust enough attention to follow the flow.
And once the flow starts, stopping it feels disruptive.
When nothing feels “off”
One of the most dangerous aspects of these messages is that nothing feels wrong while you’re reading them.
No spelling errors. No broken links. No aggressive language. No obvious red flags.
This absence of warning signs creates false confidence. People equate “no red flags” with “safe,” even though safety depends on verification, not vibes.
The most successful deception doesn’t trigger suspicion. It bypasses it.
Why smart, careful people fall for it
There’s a persistent myth that only careless users get tricked. In reality, people who are digitally active are often more exposed.
They manage multiple accounts. Use many services. Receive frequent notifications. Respond quickly to keep things running.
Efficiency becomes a habit. Pausing to question every message feels impractical.
Account-stealing messages exploit that efficiency. They don’t interrupt workflowthey disguise themselves as part of it.
The longer-term consequences
The immediate damage of account theft is obvious: loss of access, data misuse, financial risk.
But the deeper impact is erosion of trust.
After an incident, people become suspicious of legitimate messages. They hesitate. They second-guess. They experience constant low-level anxiety around communication.
Digital life becomes heavier.
This psychological cost rarely gets discussed, but it’s one of the most lasting effects.
How these messages will evolve
As users become more aware, deceptive messages adapt.
They’re getting shorter, calmer, more personalized. Less dramatic. More conversational.
Future account-stealing messages won’t look like warnings. They’ll look like updates. Reminders. Friendly check-ins.
The challenge won’t be spotting obvious dangerit will be recognizing manufactured normality.
Awareness without paranoia
Understanding these tactics doesn’t require fear. It requires perspective.
The goal isn’t to distrust everything. It’s to understand that appearance alone isn’t proof.
A message can look professional, polite, and familiarand still be designed to exploit trust.
That awareness creates space. A pause. A moment to step outside the message and consider context.
And that moment is often enough.
The quiet habit that protects you
The most effective defense isn’t technical. It’s behavioral.
It’s remembering that legitimate organizations rarely rely on a single message to secure something important. And that real security doesn’t depend on urgency delivered through convenience.
When people shift from reacting to messages to contextualizing them, deception loses its grip.
Not dramatically. Quietly.
Trust, rebuilt on better terms
Digital communication isn’t going away. And trust is still necessary.
But trust works best when it’s earned continuously, not assumed indefinitely.
Account-stealing messages succeed when trust becomes automatic. They fail when trust becomes thoughtful.
And in a digital world designed for speed, thoughtfulness is a powerful skill.
Frequently Asked Questions
What are account stealing messages exactly?
They are messages designed to look legitimate while manipulating users into giving up access credentials or verification details.
Why don’t these messages look suspicious anymore?
Because obvious warning signs no longer work. Modern deceptive messages mimic trusted communication styles closely.
Are these messages always urgent?
No. Many are deliberately calm and routine, which makes them more convincing.
Do experienced users still fall for them?
Yes. Familiarity, multitasking, and efficiency habits make even careful users vulnerable.
What’s the most reliable way to judge a message?
Not how it looks, but whether its request can be independently verified outside the message itself.